Are you ready to dive into the fascinating world of ethical hacking? Imagine yourself as a skilled white hat hacker, armed with the knowledge and expertise to safeguard the digital realm. In this article, we will explore the crucial role that white hat hackers play in cybersecurity. By understanding their methods and motivations, you will gain a deeper insight into the importance of ethical hacking in today’s interconnected world.
White hat hackers, also known as ethical hackers, utilize their skills to identify vulnerabilities in computer systems and networks. They are the unsung heroes who work tirelessly to protect us from malicious cyber threats. By following a carefully crafted methodology, these hackers not only expose weaknesses but also collaborate with security professionals and organizations to strengthen defenses.
However, ethical hacking is not without its legal and ethical considerations. We will delve into the benefits and limitations of this practice, shedding light on the complex nature of this essential cybersecurity discipline.
So, buckle up and get ready to unravel the secrets of ethical hacking.

Key Takeaways
- Ethical hacking is the practice of identifying vulnerabilities in computer systems and networks to protect digital assets and defend against cyber threats.
- White hat hackers collaborate with security professionals and possess diverse skills and knowledge in cybersecurity.
- Ethical hacking methodology involves preparing for engagements, reconnaissance and information gathering, vulnerability assessment and scanning, exploitation and penetration testing, and reporting and remediation.
- Ethical hacking helps organizations strengthen their cybersecurity defenses, identifies and addresses security weaknesses, and mitigates risks to protect sensitive data.
Introduction
Let’s dive into the exciting world of ethical hacking and uncover the crucial role of white hat hackers in safeguarding our cybersecurity.
Ethical hacking, also known as white hat hacking, is the practice of using hacking techniques to identify vulnerabilities in a system with the permission of the owner. It plays a vital role in ensuring the security of our digital infrastructure.
The main purpose of ethical hacking is to conduct a vulnerability assessment, where hackers simulate real-world attacks to identify weaknesses that malicious hackers could exploit. By doing so, white hat hackers help organizations and individuals strengthen their defenses against cyber threats.
This introductory section sets the stage for understanding the importance of ethical hacking and the critical role that white hat hackers play in maintaining the integrity and confidentiality of our digital world.

Understanding Ethical Hacking
In this discussion, you’ll gain an understanding of ethical hacking. This includes its definition and objectives.
You’ll also learn about the distinction between ethical hacking and cybercrime.
By exploring these key points, you’ll develop a clear understanding of the important role ethical hackers play in cybersecurity.
Definition and Objectives of Ethical Hacking
Definition and Objectives of Ethical Hacking:

Ethical hacking, with its goal of identifying vulnerabilities and strengthening cybersecurity, can be likened to a symphony conductor guiding the orchestra of digital defenses.
White hat hackers, the heroes of this digital realm, play a crucial role in ensuring the security of computer systems and networks. They use their skills and knowledge to proactively discover weaknesses and prevent malicious attacks.
To become proficient in this field, individuals can attend hacker camps or enroll in ethical hacking classes. These educational opportunities provide hands-on training and teach participants various hacking techniques and methodologies.
Hacker studies involve analyzing system vulnerabilities, exploiting security loopholes, and suggesting remedial measures. By actively engaging in ethical hacking, these experts contribute to the overall protection of digital assets and help organizations stay one step ahead of cybercriminals.

Distinction between Ethical Hacking and Cybercrime
There’s a clear distinction between ethical hacking and cybercrime. Ethical hacking, also known as white hat hacking, aims to protect digital assets. It plays a vital role in cybersecurity by identifying vulnerabilities in computer systems, networks, and applications. White hat hackers work with the permission of the system owner to fix weaknesses and enhance security.
On the other hand, cybercrime involves illegal activities such as unauthorized access, data theft, and system disruption. Cybercriminals exploit vulnerabilities for personal gain or to cause harm.
Understanding this distinction is crucial in the fight against cyber threats. Ethical hacking ensures that organizations stay one step ahead of cybercriminals, protecting sensitive data and maintaining the integrity of digital systems.
The Role of White Hat Hackers
In this discussion, you’ll explore the definition and characteristics of white hat hackers.
You’ll also delve into the skills and expertise required to be a white hat hacker, as well as the legal and ethical boundaries they must adhere to.
Understanding these aspects will give you a comprehensive understanding of the role white hat hackers play in cybersecurity.
Definition and Characteristics of White Hat Hackers
White hat hackers, also known as ethical hackers, possess a diverse set of skills and knowledge in the field of cybersecurity. They play a crucial role in ethical hacking, as they use their skills to identify vulnerabilities in computer systems and networks, helping organizations strengthen their cybersecurity defenses.
Did you know that 87% of white hat hackers have a bachelor’s degree or higher? This statistic highlights the importance of education and expertise in this profession.

White hat hackers have a strong sense of ethics and adhere to strict guidelines. They ensure that they only access systems with proper authorization and for legitimate purposes.
These hackers are skilled in various programming languages, network protocols, and operating systems. This allows them to understand the intricacies of different systems and effectively evaluate their security.
White hat hackers constantly update their knowledge and keep up with the latest cybersecurity trends. This makes them invaluable assets in the ongoing battle against cyber threats.
Skills and Expertise of White Hat Hackers
White hat hackers bring a plethora of skills and expertise to the table, allowing them to navigate the intricacies of computer systems and networks, ensuring they can effectively identify vulnerabilities and strengthen cybersecurity defenses.

These ethical hacking experts possess a deep understanding of programming languages, such as C++, Python, and Java, enabling them to comprehend complex code structures and identify potential weak points.
Additionally, they possess exceptional problem-solving skills, enabling them to think critically and creatively to find innovative solutions to security challenges.
Their expertise extends to areas such as network protocols, cryptography, and penetration testing techniques, which they utilize to uncover vulnerabilities before malicious actors can exploit them.
With their diverse skill set and extensive knowledge, white hat hackers play a crucial role in safeguarding our digital world from cyber threats.

Legal and Ethical Boundaries for White Hat Hackers
Picture yourself as a brilliant detective, carefully treading the thin line between legality and security, as a white hat hacker in the world of ethical hacking.
White hat hackers play a crucial role in cybersecurity by uncovering vulnerabilities in systems and networks, ultimately strengthening their defenses. However, they must be aware of both legal and ethical boundaries while conducting their work.
Legally, white hat hackers must obtain proper authorization before performing any hacking activities, ensuring they are not crossing any legal lines.
Ethically, they must use their skills and expertise responsibly, avoiding any malicious intent or harm. It is important for white hat hackers to prioritize the protection of individuals and organizations, respecting privacy and confidentiality.

By adhering to these boundaries, white hat hackers contribute to a safer and more secure digital world.
Ethical Hacking Methodology
In this subtopic, you’ll explore the ethical hacking methodology. You’ll learn about the key steps involved in ethical hacking engagements, including:
- Preparing for the engagements
- Conducting reconnaissance and information gathering
- Performing vulnerability assessment and scanning
- Executing exploitation and penetration testing
- Reporting and remediation
By understanding and following this methodology, you’ll be equipped to effectively identify and address security vulnerabilities in systems and networks.
Preparing for Ethical Hacking Engagements
To effectively prepare for ethical hacking engagements, you need to ensure you have the proper authorization and permissions in place, allowing you to define the scope of the engagement and ultimately protect against potential cybersecurity threats.

As a white hat hacker, it is crucial to obtain explicit permission from the organization you are working with. This authorization ensures that you are legally allowed to conduct your ethical hacking activities and prevents any misunderstandings or legal issues down the line.
Additionally, defining the scope of the engagement is essential to ensure that you focus on specific areas of concern and avoid any unnecessary intrusion. By clearly outlining the goals and limitations of the engagement, you can maximize the effectiveness of your ethical hacking efforts and provide valuable insights to enhance cybersecurity measures.
Always remember that preparing properly for ethical hacking engagements is fundamental to maintain the integrity and ethical standards of the white hat hacker community.
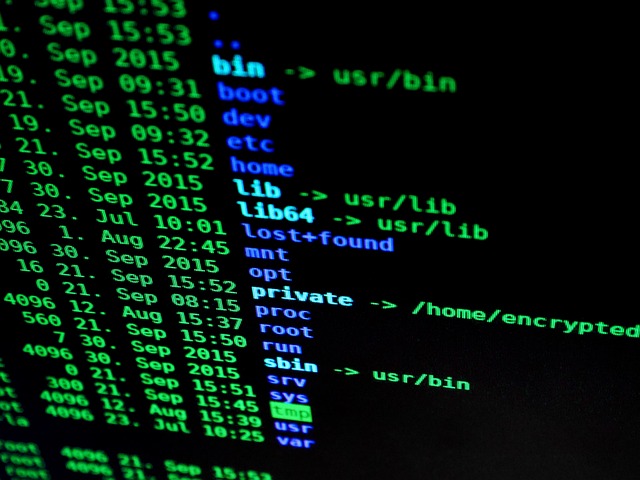
Reconnaissance and Information Gathering
Gathering relevant information about the target system is like peeling back the layers of an onion, revealing hidden vulnerabilities and potential entry points. In the world of ethical hacking, this step is crucial for a white hat hacker to understand the target system’s weaknesses and devise effective countermeasures.
Reconnaissance and information gathering play a vital role in cybersecurity, as they allow hackers to gather intelligence about the target’s network infrastructure, software, and potential vulnerabilities. By conducting thorough reconnaissance, ethical hackers can identify weak points and potential exploits before malicious actors can exploit them. This proactive approach helps organizations strengthen their defenses and protect their valuable data.
With the ever-evolving landscape of cybersecurity, reconnaissance and information gathering remain essential tools in the white hat hacker’s arsenal to stay one step ahead of potential threats.
Vulnerability Assessment and Scanning
Vulnerability assessment and scanning play a crucial role in cybersecurity. They involve systematically analyzing a system to identify weaknesses that could be exploited by malicious actors. White hat hackers, also known as ethical hackers, specialize in this process and use various scanning techniques to uncover potential vulnerabilities. These vulnerabilities could include outdated software, misconfigurations, or weak passwords. By conducting thorough assessments and scans, white hat hackers provide valuable insights into the system’s security posture. This proactive approach helps organizations strengthen their defenses and prevent cyberattacks. It’s like shining a flashlight into the dark corners of a room to uncover any lurking threats. With their expertise, white hat hackers ensure that systems remain secure and protected against potential threats.
Exploitation and Penetration Testing
When you delve into the world of exploitation and penetration testing, you’ll discover the exhilarating art of uncovering vulnerabilities and outsmarting potential attackers, like a master chess player anticipating their opponent’s moves.
In the realm of ethical hacking, the role of a white hat hacker is crucial in ensuring cybersecurity. Penetration testing involves simulating real-world attacks to identify weaknesses in a system’s defenses. It requires a deep understanding of various exploit techniques and tools to infiltrate and gain unauthorized access to a network or application.
The goal is not to cause harm, but rather to expose vulnerabilities and provide recommendations for strengthening security measures. By conducting thorough exploitation testing, white hat hackers play a vital role in helping organizations identify and address potential security risks, ultimately safeguarding valuable data and systems from malicious cyber threats.
Reporting and Remediation
Now that you understand the process of exploitation and penetration testing, it’s time to move on to the crucial next step: reporting and remediation.
As an ethical hacker, your role is not just to identify vulnerabilities, but also to document your findings and recommend security improvements.
Reporting is a critical aspect of ethical hacking as it allows organizations to understand the risks they face and take necessary actions to protect their systems.
Your comprehensive report will outline the vulnerabilities discovered, their potential impact, and provide clear recommendations for remediation.
By doing so, you play a vital role in strengthening cybersecurity defenses and ensuring that organizations are well-equipped to defend against cyber threats.
So, let’s dive into the reporting and remediation phase and make a significant impact in the world of ethical hacking and cybersecurity.
Importance of Ethical Hacking in Cybersecurity
In the field of cybersecurity, ethical hacking plays a crucial role. It helps identify and address security weaknesses. Ethical hackers actively seek out vulnerabilities and help organizations patch them up before they are exploited.
Ethical hacking also strengthens defense mechanisms. It tests the effectiveness of existing security measures and suggests improvements. This helps organizations stay one step ahead of potential threats.
Furthermore, ethical hacking assists in regulatory compliance and risk management. It ensures that organizations meet industry standards and guidelines. This minimizes potential legal and financial risks.
Identifying and Addressing Security Weaknesses
Addressing security weaknesses involves identifying vulnerabilities and patching them up to ensure a solid defense against potential cyber threats. Ethical hacking plays a crucial role in this process.

A white hat hacker, also known as an ethical hacker, is skilled in identifying security weaknesses in computer systems and networks. Their expertise lies in proactively testing and analyzing the security infrastructure to find vulnerabilities before malicious hackers exploit them. By employing ethical hackers, organizations can stay one step ahead in the ever-evolving field of cybersecurity.
These experts use a variety of tools and techniques to uncover weaknesses in software, hardware, and network configurations. Once identified, the vulnerabilities can be addressed promptly to strengthen the overall security framework.
Ethical hacking is an essential component of cybersecurity, as it helps organizations mitigate risks and protect sensitive data from potential breaches.
Strengthening Defense Mechanisms
Take a moment to imagine the feeling of complete confidence and peace of mind that comes from knowing your defense mechanisms are impenetrable, safeguarding your valuable assets from any potential cyber threats.

This is the goal of strengthening defense mechanisms in cybersecurity. Ethical hacking plays a crucial role in this process. White hat hackers, armed with their expertise and knowledge, use vulnerability assessment tools to identify weaknesses in your system. They then work alongside your team to address these vulnerabilities, strengthening your defense mechanisms.
By proactively identifying and fixing these weaknesses, you can stay one step ahead of potential attackers. Ethical hacking helps create a robust cybersecurity framework, ensuring that your valuable assets are protected from any cyber threats that may come your way.
Assisting in Regulatory Compliance and Risk Management
Ensure your organization’s regulatory compliance and manage risks effectively by leveraging the assistance provided by ethical hackers.
These white hat hackers play a crucial role in the field of cybersecurity, helping organizations stay on top of regulatory requirements and minimize potential risks.

By conducting thorough assessments and penetration testing, ethical hackers identify vulnerabilities in your systems and networks, ensuring compliance with industry standards and regulations.
They work closely with your team to analyze and address any weaknesses, providing valuable insights into potential risks and suggesting appropriate mitigation strategies.
With their expertise, ethical hackers help you stay one step ahead of cyber threats, protecting your sensitive data and ensuring a secure environment.
By partnering with these professionals, you can confidently navigate the complex landscape of regulatory compliance and effectively manage the risks associated with cybersecurity.

Skills and Certifications for Ethical Hackers
To become an ethical hacker, you need to possess strong technical skills and knowledge in areas like computer networking, programming languages, and operating systems. These skills will enable you to understand the vulnerabilities and weaknesses in systems that can be exploited.
Additionally, obtaining ethical hacking certifications such as Certified Ethical Hacker (CEH) or Offensive Security Certified Professional (OSCP) can validate your expertise and enhance your credibility in the field.
Technical Skills and Knowledge
Mastering the art of ethical hacking requires a vast array of technical skills and knowledge. To become a proficient white hat hacker, you need to excel in operating systems, networks, and security tools.
By enrolling in an ethical hacking course or pursuing a certified ethical hacker certification, you can gain the necessary expertise. These training programs provide in-depth knowledge on operating systems, network protocols, and various security tools. You will learn how to navigate different operating systems, understand network infrastructure, and effectively use security tools to identify vulnerabilities.

Additionally, these courses cover topics like cryptography, web application security, and penetration testing. By acquiring technical skills and knowledge through ethical hacking training, you can become a skilled white hat hacker capable of safeguarding against cyber threats.
Ethical Hacking Certifications
Ready to take your cybersecurity skills to the next level? Consider pursuing one of the popular certifications for ethical hackers, such as CEH or OSCP.
Becoming a certified ethical hacker (CEH) is a great way to demonstrate your expertise in ethical hacking and gain recognition in the cybersecurity field. CEH courses cover a wide range of topics, such as network security, web application security, and penetration testing. These courses provide hands-on experience and practical knowledge that can be directly applied to real-world scenarios.
Another popular certification is the Offensive Security Certified Professional (OSCP), which focuses on practical skills and requires a rigorous exam that tests your ability to exploit vulnerabilities in systems.

By obtaining these ethical hacking certifications, you can enhance your career prospects and contribute to the growing field of cybersecurity.
Collaboration with Security Professionals and Organizations
When it comes to collaboration between ethical hackers and security teams, it is crucial for both parties to work together to ensure the highest level of cybersecurity.
By sharing knowledge and expertise, ethical hackers can help security teams identify vulnerabilities and implement effective countermeasures.
Bug bounty programs and responsible disclosure are also important aspects of this collaboration, as they provide a platform for ethical hackers to report vulnerabilities and receive recognition for their efforts, ultimately leading to a safer digital environment for all.

Collaboration between Ethical Hackers and Security Teams
Collaboration between ethical hackers and security teams is crucial. It requires effective communication and mutual trust to ensure a successful partnership in defending against cyber threats.
Ethical hacking plays a vital role in cybersecurity. White hat hackers use their skills to identify vulnerabilities in systems and networks, helping security teams strengthen their defenses.
By working together, ethical hackers and security teams can share knowledge and expertise. This allows for a more comprehensive and proactive approach to cybersecurity.
This collaboration enables security teams to understand potential attack vectors and develop effective countermeasures. It also provides ethical hackers with the necessary resources and support to carry out their assessments and investigations.

Ultimately, this partnership helps organizations stay one step ahead of cybercriminals. It ensures the protection of sensitive data and maintains the integrity of systems and networks.
Bug Bounty Programs and Responsible Disclosure
Get ready to be rewarded for your valuable contributions to security by participating in bug bounty programs and practicing responsible disclosure.
Ethical hacking, carried out by white hat hackers, plays a crucial role in enhancing cybersecurity. Bug bounty programs are designed to encourage ethical hackers to identify vulnerabilities in software, websites, or systems by offering them rewards or bounties.
By participating in these programs, you have the opportunity to contribute to the improvement of security measures and protect against potential threats.

Responsible disclosure is also an important aspect of ethical hacking, ensuring that vulnerabilities are reported to the appropriate authorities or organizations in a responsible and ethical manner.
This collaboration between ethical hackers and security teams is essential to maintain the integrity and safety of digital systems in today’s interconnected world.
So, why not join the community of ethical hackers and contribute to the ever-evolving field of cybersecurity?
Legal and Ethical Considerations
In this subtopic, you’ll explore the importance of adhering to laws and regulations, ethical guidelines, and professional codes of conduct in cybersecurity.

These frameworks help ensure that security professionals operate within legal boundaries and maintain the highest standards of ethical behavior.
By understanding and upholding these principles, you’ll be better equipped to navigate the complex landscape of cybersecurity and contribute to a safer digital environment.
Adherence to Laws and Regulations
Ensuring compliance with laws and regulations is a crucial aspect of the work of white hat hackers. They must understand and comply with applicable legal frameworks, such as the General Data Protection Regulation (GDPR) and the Computer Fraud and Abuse Act (CFAA). By adhering to these laws and regulations, white hat hackers ensure that their actions remain within legal boundaries while providing valuable insights to organizations. This helps organizations improve their cybersecurity measures and protect sensitive data. White hat hackers play the role of cybersecurity guardians, safeguarding digital landscapes from potential threats. Ethical hacking is a practice that involves identifying vulnerabilities in computer systems and networks to strengthen their security. White hat hackers, also known as ethical hackers, use their skills and knowledge to protect organizations from cyberattacks.
Ethical Guidelines and Professional Codes of Conduct
Now that you understand the importance of adherence to laws and regulations in the field of ethical hacking, let’s delve into another crucial aspect: ethical guidelines and professional codes of conduct.
In the world of cybersecurity, it is imperative for white hat hackers to uphold the highest ethical standards. These guidelines and codes of conduct serve as a moral compass, ensuring that their actions are always in line with the principles of integrity, privacy, and respect for others.
By following these ethical guidelines, white hat hackers are able to navigate the complex terrain of cybersecurity while maintaining the trust of their clients and the broader society. These guidelines provide a framework for responsible and accountable behavior, ensuring that the actions of ethical hackers contribute to the overall security and well-being of individuals, organizations, and the digital landscape as a whole.
Benefits and Limitations of Ethical Hacking
When it comes to ethical hacking, there are several benefits for organizations and businesses. By conducting ethical hacking practices, companies can identify and address vulnerabilities in their systems, thereby strengthening their overall cybersecurity posture.
However, it is important to note that there are also limitations and challenges in ethical hacking. One of the main limitations is the need for skilled professionals. Ethical hacking requires individuals with extensive knowledge and expertise in cybersecurity, which can be difficult to find and hire.

Another limitation is the potential legal and ethical concerns. Ethical hackers must ensure that they are operating within the boundaries of the law and ethical guidelines. This can sometimes be a complex and delicate balance, as they need to exploit vulnerabilities without causing harm or breaching privacy.
Furthermore, ethical hacking faces the constant evolution of hacking techniques. As hackers continue to develop new and sophisticated methods, ethical hackers must constantly update their skills and knowledge to stay ahead of the game.
In conclusion, while ethical hacking offers numerous benefits for organizations, such as identifying vulnerabilities and strengthening cybersecurity, it also comes with limitations and challenges. These include the need for skilled professionals, potential legal and ethical concerns, and the ever-evolving nature of hacking techniques.
Benefits for Organizations and Businesses
By leveraging the skills of white hat hackers, your organization can unlock a world of benefits. These benefits include enhanced security measures and a proactive defense against potential threats.

Ethical hacking, performed by these skilled professionals, plays a crucial role in cybersecurity for organizations. With their expertise, they can identify vulnerabilities in your systems and networks before malicious actors exploit them. This allows you to patch those weaknesses and strengthen your overall security posture.
Additionally, white hat hackers can conduct penetration testing to simulate real-world attacks and assess your organization’s resilience. By doing so, they provide valuable insights into potential weaknesses and help you prioritize security investments.
Moreover, ethical hacking helps you comply with industry regulations and standards, ensuring that your organization maintains a robust cybersecurity framework.
Ultimately, by embracing the benefits of ethical hacking, your organization can proactively protect itself from cyber threats and stay one step ahead of potential attackers.

Limitations and Challenges in Ethical Hacking Practices
However, it’s important to acknowledge the limitations and challenges that arise in the practice of ethical hacking.
While white hat hackers play a crucial role in cybersecurity, there are certain limitations they face. Firstly, ethical hacking can be time-consuming and resource-intensive. It requires extensive knowledge and expertise to identify vulnerabilities and potential threats.
Additionally, there is a constant need for continuous learning and staying updated with the latest hacking techniques and technologies.
Moreover, ethical hacking can sometimes be legally challenging, as hackers need to ensure they are operating within legal boundaries and obtaining proper authorization.

Furthermore, there is a risk of unintentional damage or disruption to systems during the hacking process.
Despite these challenges, ethical hacking remains an essential practice in safeguarding organizations and businesses from malicious attacks, highlighting the need for ongoing support and recognition for white hat hackers.
Conclusion
Ethical hackers play a crucial role in maintaining the security of systems and protecting against cyber threats. Ethical hacking, performed by white hat hackers, is a proactive approach to cybersecurity that helps identify vulnerabilities and weaknesses in systems. These hackers use their skills and knowledge to simulate real-world cyber attacks, allowing organizations to patch vulnerabilities before malicious hackers exploit them.
By conducting ethical hacking practices, businesses can enhance their security measures and ensure the confidentiality, integrity, and availability of their data. It is important to recognize the invaluable contribution of white hat hackers in the fight against cyber threats. Their expertise and ethical practices serve as a shield, safeguarding organizations from potential breaches and ensuring the overall resilience of the cybersecurity landscape.

So, embrace the role of white hat hackers and prioritize ethical hacking practices to bolster your system’s security.
Ethical hacking plays a pivotal role in bolstering cybersecurity.
White hat hackers, with their expertise and ingenuity, actively contribute to the protection of digital systems.
Through their meticulous methodology, they uncover vulnerabilities and provide valuable insights for safeguarding sensitive information.
Collaboration with security professionals and organizations enhances their effectiveness in combating cyber threats.
However, it is crucial to navigate legal and ethical considerations to ensure responsible hacking practices.
While ethical hacking has its benefits, it also has limitations.
Nevertheless, the remarkable efforts of white hat hackers contribute to a safer digital landscape.
You might also like to read on these cybersecurity articles on Get Hitch
The Dark Web Unveiled: Understanding Its Risks and How to Navigate Safely
Cybersecurity for Small Businesses: Protecting Your Company from Cyber Threats