 If you’ve ever heard of CERT-IN, you may be wondering what this organization does. What are its mandates? How does it help organizations secure their networks? CERT-In is a government mandated organization that develops security guidelines and advisories for organizations. In addition to that, it has also forged MoUs with similar organisations around the world. Read on to learn more about CERT-In.
If you’ve ever heard of CERT-IN, you may be wondering what this organization does. What are its mandates? How does it help organizations secure their networks? CERT-In is a government mandated organization that develops security guidelines and advisories for organizations. In addition to that, it has also forged MoUs with similar organisations around the world. Read on to learn more about CERT-In.
CERT-In is a government-mandated organization
The Indian Computer Emergency Response Team (CERT-In) is a government-mandated organization that responds to major incidents involving the use of computers. CERT-In has been operating in India since 2004 and is mandated by the 2008 Information Technology Amendment Act to help establish holistic IT security policies. There are many CERT organizations around the world, but CERT-In is unique in that it was established by a government-authorized organization. The majority of these teams operate independently, with only a small number of coordinated activities.
CERT-In provides security guidelines
CERT-In is a government-approved organization that focuses on information security. Each country has its own institution to address information security concerns, and India is no different. India’s CERT-In oversees the nation’s cyber security matters. The organization’s primary mission is to be a trusted partner to those affected by cybersecurity incidents. However, the new directions it’s taking have a negative impact on the collaborative nature of the organization. The new requirement for reporting incidents in six hours can easily overwhelm CERT-In’s capacity.
CERT-In issues advisories
While the IT industry is accustomed to the quarterly security updates issued by the Federal Trade Commission, the increasing number of cybersecurity incidents has led to a rise in CERT-In advisories. The agency works to protect the public from cyber incidents by investigating and producing vulnerability analysis, alerts, and advisories. CERT-In reports are published every two and a half minutes and have been increasing in frequency with new products and versions.
CERT-In has signed MoUs with similar organisations
CERT-In has signed MoUs in seven countries to cooperate on computer security. The MoUs will facilitate information sharing and technical assistance in security issues and would enable the two organisations to implement a programme aimed at educating the cyber community and enhancing internet security. The two institutions already have a close relationship as CERT-In provides valuable information on computer security and advises network administrators and users on best practices for secure computing.
Forensics and investigation support
The CERT-In focuses on forensic and investigation support, as well as the scientific elements of the criminal justice process. This certificate is designed to provide students with immediate application in a variety of settings, including local police stations, municipalities, social support organizations, businesses, and governmental agencies. CERT-In’s interdisciplinary approach to forensics explores the various notions behind criminal investigation.
There are many technologies and protocols used to provide secure identity management and authorization. Two of the most prominent are the SAML and OpenID Connect protocols. Both of these protocols use a common set of attributes to verify an identity. If the identity of a person is stolen, it can result in bank account fraud. Identity theft is a problem that is increasingly becoming a serious concern because it can lead to serious consequences. Also read Why Using a VPN While Traveling Is Essential
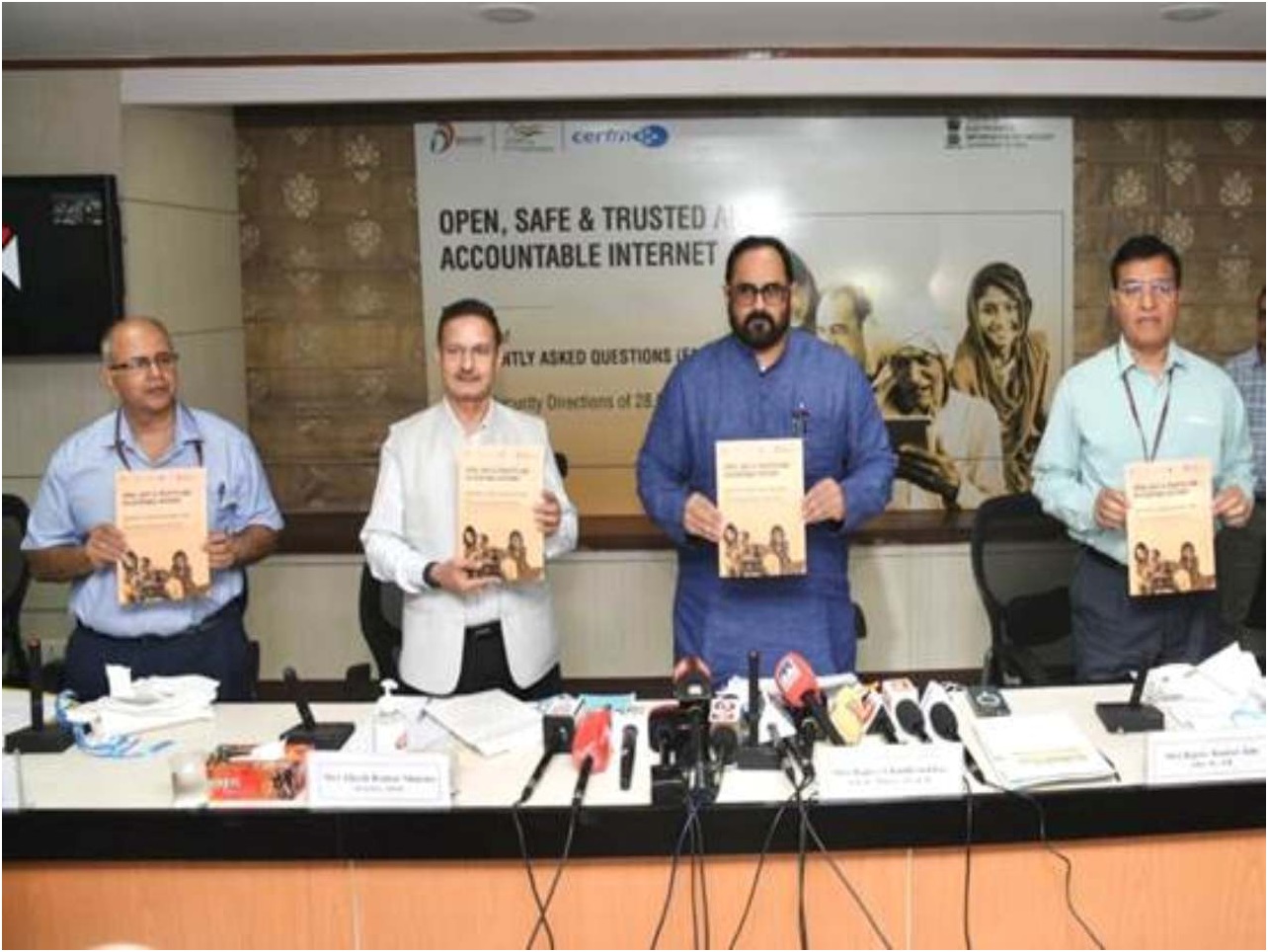
On April 28, 2022, the Indian Computer Emergency Response Team (CERT-IN) issued fresh directions in relation to information security practices, procedures, prevention, response, and reporting of cyber incidents. Given increasing digitisation and frequent reports of user databases being available for sale, efforts to improve reporting of cyber security incidents are required. However, these directions, issued without any public consultation, include mandates for overbroad data collection and data retention, vague technical requirements and penal provisions for non-compliance. With directions slated to go into effect after June 27, 2022, pressing concerns about what they mean for VPN services and anonymity-preserving services like TOR remain.
In this conversation, IFF staffers Tejasi Panjiar, Prateek Waghre and Mr. Srinvas Kodali, researcher with the Free Software Movement of India, will talk about their concerns related to surveillance and data retention beyond need or purpose.







